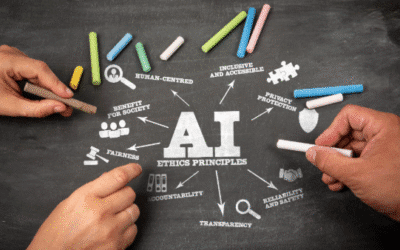
Managing ChatGPT and other AI tools isn't just about staying compliant; it's about keeping control and earning client trust. Follow these five rules to set smart, safe, and effective AI boundaries in your organization. Set Clear Boundaries Before You Begin Always Keep...
Month: February 2026
Time for a Quiz: Is Your Company Safe from Phishing Scams?
As you have read in our previous blogs, we have covered phishing attacks over the past three weeks. We have discussed what they look like, the warning indications of an attack, and some precautions you should take to safeguard your company. One thing—and a very...
Phishing Scams and Social Engineering Tactics
Social engineering is a popular term in the cybersecurity industry. What is it, though, and why are companies so terrified? It is a type of hacking that induces victims to provide information by tricking and manipulating them. Social engineering tactics have caused a...
Insider Threats and How to Avoid Becoming One
When people hear the term insider threat, they often imagine a disgruntled employee deliberately trying to harm their company. While that can happen, the reality is much harder to detect and avoid. An insider threat encompasses any security risk that comes from...
Are Phishing Scams Getting Harder to Recognize?
One of the biggest shifts that we can expect to see in cybersecurity this year, is how ordinary cyberattacks will appear. Instead of obvious scams filled with spelling mistakes or strange links, many attacks will blend seamlessly into the rest of your messages....
The “Deepfake CEO” Scam: Why Voice Cloning is the Next Cyber Threat
The phone rings, and it’s your boss. The voice is unmistakable; with the same flow and tone you’ve come to expect. They’re asking for a favor: an urgent wire transfer to lock in a new vendor contract, or sensitive client information that’s strictly confidential....